In 2013, the Westmore Information, a tiny newspaper serving the suburban neighborhood of Rye Brook, New York, ran a aspect on the opening of a sluice gate at the Bowman Avenue Dam. Costing some $2 million, the new gate, then nearing completion, was developed to reduce flooding downstream.
The celebration caught the eye of a number of nearby politicians, who gathered to shake fingers at the official unveiling. “I have been to heaps of ribbon-cuttings,” county executive Rob Astorino was quoted as stating. “This is my initially sluice gate.”
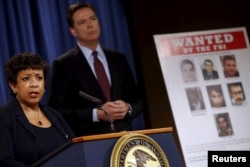
But locals apparently weren’t the only types with their eyes on the dam’s new sluice. According to an indictment handed down late last week by the U.S. Section of Justice, Hamid Firoozi, a perfectly-identified hacker dependent in Iran, received obtain a number of moments in 2013 to the dam’s handle systems. Had the sluice been absolutely operational and related to those systems, Firoozi could have created serious destruction. The good thing is for Rye Brook, it was not.
Hack assaults probing important U.S. infrastructure are very little new. What alarmed cybersecurity analysts in this circumstance, on the other hand, was Firoozi’s apparent use of an old trick that computer nerds have quietly regarded about for yrs.
It truly is called “dorking” a look for motor — as in “Google dorking” or “Bing dorking” — a tactic very long used by cybersecurity experts who get the job done to near protection vulnerabilities.
Now, it seems, the hackers know about it as perfectly.
Hiding in open view
“What some call dorking we really connect with open-source community intelligence,” explained Srinivas Mukkamala, co-founder and CEO of the cyber-chance evaluation firm RiskSense. “It all is dependent on what you question Google to do.”
Mukkamala states that research engines are constantly trolling the Online, on the lookout to file and index each product, port and distinctive IP tackle linked to the Web. Some of people points are designed to be community — a restaurant’s homepage, for example — but a lot of other people are meant to be private — say, the protection digital camera in the restaurant’s kitchen. The challenge, suggests Mukkamala, is that too a lot of folks do not realize the change ahead of likely on line.
“There is certainly the World-wide-web, which is nearly anything that’s publicly addressable, and then there are intranets, which are meant to be only for inner networking,” he advised VOA. “The research engines never care which is which they just index. So if your intranet isn’t really configured properly, that’s when you start off looking at details leakage.”
When a restaurant’s closed-circuit digital camera could not pose any real safety threat, lots of other items getting related to the World-wide-web do. These contain tension and temperature sensors at ability vegetation, SCADA programs that regulate refineries, and operational networks — or OTs — that continue to keep important production crops functioning.
Regardless of whether engineers know it or not, numerous of these things are staying indexed by search engines, leaving them quietly hiding in open up check out. The trick of dorking, then, is to figure out just how to find all all those assets indexed on the internet.
As it turns out, it truly is truly not that really hard.
An uneven risk
“The matter with dorking is you can create custom made searches just to glimpse for that info [you want],” he said. “You can have many nested research disorders, so you can go granular, permitting you to find not just every solitary asset, but each other asset that is related to it. You can actually dig deep if you want,” said RiskSense’s Mukkamala.
Most major look for engines like Google present sophisticated research features: commands like “filetype” to hunt for certain forms of data files, “numrange” to discover certain digits, and “intitle,” which appears for exact web site text. Furthermore, diverse look for parameters can be nested a single in one more, making a incredibly high-quality electronic web to scoop up information and facts.
For example, in its place of just getting into “Brook Avenue Dam” into a research motor, a dorker could possibly use the “inurl” operate to hunt for webcams on the internet, or “filetype” to glimpse for command and control paperwork and features. Like a scavenger hunt, dorking entails a certain total of luck and persistence. But skillfully applied, it can greatly boost the probability of acquiring one thing that need to not be community.
Like most points on line, dorking can have optimistic utilizes as nicely as damaging. Cybersecurity specialists significantly use these kinds of open-supply indexing to uncover vulnerabilities and patch them just before hackers stumble upon them.
Dorking is also absolutely nothing new. In 2002, Mukkamala states, he worked on a project exploring its prospective threats. Much more just lately, the FBI issued a public warning in 2014 about dorking, with guidance about how community administrators could protect their units.
The issue, suggests Mukkamala, is that almost everything that can be linked is getting hooked up to the World-wide-web, normally without regard for its stability, or the security of the other objects it, in switch, is connected to.
“All you need is one particular vulnerability to compromise the method,” he told VOA. “This is an uneven, widespread risk. They [hackers] don’t want just about anything else than a notebook and connectivity, and they can use the instruments that are there to get started launching attacks.
“I never imagine we have the understanding or resources to protect from this risk, and we are not ready.”
That, Mukkamala warns, usually means it is far more probably than not that we’ll see a lot more instances like the hacker’s exploit of the Bowman Avenue Dam in the many years to appear. Regrettably, we may possibly not be as fortunate the up coming time.







More Stories
Navigating the World of Insurance: Road Tax Renewal with Pos Malaysia
Navigating Malaysia’s Road Tax Landscape: Pos Malaysia’s Digital Frontier
Transformative Magic Mushroom Retreat: Experience Mental and Emotional Healing with Life Synergy Retreats